Recently, I enabled passwordless authentication on my Microsoft account. This was certainly easier than typing in a 20-30 character password. Using a password manager makes it easier, but at times I have had to actually type all of the characters. What a chore that was!
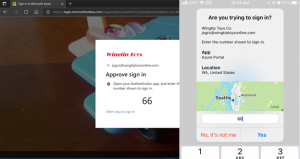
Those who enable phone sign-in from Microsoft Authenticator will see a message that asks them to tap a number in their app. No username or password is asked for. To complete the sign-in process in the app, a user must next take the following actions:
- Enter the number they see on the login screen into Microsoft Authenticator dialog.
- Choose Approve.
- Provide their PIN or biometric.
Scary Experience
Let me tell you about an experience that I had recently. I knew I had this turned on and I know that there are always failed login attempts. Many don’t have visibility into their email logins. Here are some recent logins that have been redacted:
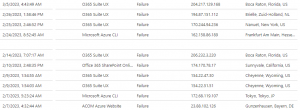
Unless you review the logs or receive alerts you will not notice the failed login attempts. What if you saw failed and successful login attempts from countries your employees are not working or traveling to? We have seen them from all over the world among our partners. Seeing failed login attempts is normal and expected.
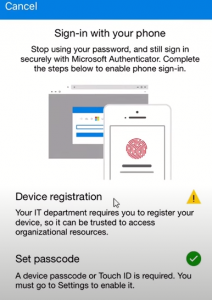
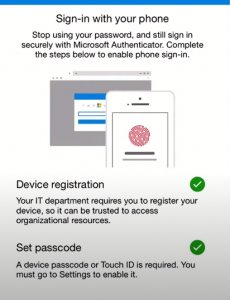
Recall, I enabled passwordless login which is different because you enable phone sign-in and register your device as listed below. Once it is registered, a password will no longer be required. Now the login experience will require you to enter your email and then a push notification will be sent to your phone.
Perhaps you are beginning to understand why I was startled when I received an approval notification early March, from a location in Europe that turned out to be a Tor browser exit from the dark web. I was in the process of logging into another account and approvals were coming in. However, this one was different because we made sure to include the application and the location on the approval notification. Once I saw the location, I started to panic a bit. I had forgotten that I setup passwordless authentication and I immediately thought my unique password had been compromised. If this was the case, it would mean that I had succumbed to:
- a possible man-in-the middle attack
- a compromised browser that resulted in the above
- some sort of initial access
Either way, steps were taken to access and better understand what had happened. This meant, reviewing the and auditing logs and experiencing that feeling that something could have happened. There could have been several scenarios that could have led to compromise but there was no compromise.
- Passwordless was turned off for now
- Logs were reviewed
- All active sessions were disconnected
- A new unique password was made
- Location-based Conditional Access was reenabled
- What-If testing was done
It was a lesson learned indeed. Preventing logins from certain locations has been a standard policy for all our partners. The truth of the matter, threat actors will attempt to login at you hoping to gain initial access. Getting the notification without me prompting it was odd. It is evident that I am not ready for passwordless yet until we finish implementing strong phishing resistant MFA on the company accounts.
If you ever receive a notification resulting from a login attempt that you did not initiate, then you need to proper action and report it to your IT security department, whether in-house our outsourced. If you care for it yourself, make sure you take steps sufficient to ensure that there was no compromise and secure your accounts.







